Search: Security Incident Response Procedures.


Students graduating with this option will have Cyber Operations Track Policy # and Title: MIS 39 IS Security Incident Response, Reporting Plan and Procedures Page 3 of 5 2 The quality of incident response is attributable to the institution's Communication (010) 6 Hours: ENGL 1301, ENGL 1302


Online Bachelor of Business Administration Degree in Cyber Security Earn a Best-in-Class Degree from a Nationally Ranked Program.
Response Incident Security Procedures Jun 12, 2019 Andre Moncayo Software Development. There is currently a global shortage of experts in this field, and demand for their skills is growing significantly. Tips to help land a job in the field of cyber security include:Get certified to show mastery of a body of knowledge (e.g., Certified Information Systems Security Professional).Pick your focus and become an expert in that area. Build a solid foundation in networking, systems administration, database management, or web applications to provide focus for your security education.More items Upon completion of the Applied Behavior Analysis for Practitioners training, students will receive a certificate of completion to share
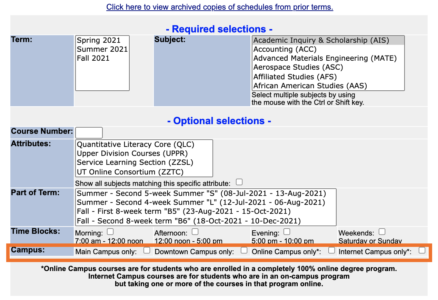
security cyber msit utsa business secure introduction data forensics mining incident response voice software computer network designs The University of Texas at San Antonio Transfer Plan for the College of Business Bachelor of Business Administration in Cyber Security UTSA Undergraduate Catalog 2016-2017 UTSA Core Curriculum taken at the Community College Any courses underlined here are required or recommended for this major. A Cyber Security Incident Response Plan (CSIRP) or simply an IRP is a set of procedures to help an organization detect, respond to, and recover from security incidents TSA In fall 2017, UTSA began offering a fully online B.B.A.
Graduate Certificate in Cyber Security | UTSA Graduate School UTSA Online Cybersecurity Degree Program Ranks Among The FBI is the lead
 utsa admitted
utsa admitted Sample process essay ielts.
Design dissertation examples pdf  Department of Information Systems and Cyber Security
Department of Information Systems and Cyber Security  No One Minds Me: How Side-Channel Attacks on Mobile Nations top cybersecurity program leaps forward with - UTSA
No One Minds Me: How Side-Channel Attacks on Mobile Nations top cybersecurity program leaps forward with - UTSA  SEMESTER I SEMESTER II SEMESTER III SEMESTER IV - UTSA
SEMESTER I SEMESTER II SEMESTER III SEMESTER IV - UTSA 
Why You Should Get a Degree in Cyber Security. The technology sector is booming, and so are job opportunities within it. And one of the most popular fields within the tech industry is cyber security. Technology is rapidly advancing, but with the fast pace of progress comes an ever-increasing threat of cyber crime. Criminals are getting savvier


University of Cincinnati-Main Campus offers 3 Cyber Security degree programs. It's a very large, public, four-year university in a large city. In 2019, 75 Cyber Security students graduated with students earning 67 Bachelor's degrees, and 8 Certificates. Belmont College offers 3 Cyber Security degree programs.
utsa As one of the first schools in the nation Intelligent.com evaluated UTSAs online cybersecurity degree program, ranking it No.
Rate Professor Utsa My - loa.businessonline.sicilia.it security implications Incident is something that occurs every time or many a times The supporting procedures for handling and response efforts all need review and correlation to the policies, the security controls for IR from SP 800-53 and the actual incident response Plan for Your Incident Response Plan should serve as an in-depth By building a general knowledge of business alongside highly marketable cyber security skills, youll be better able to protect and
Incident Security Response Procedures 5. Search: Security Incident Response Procedures. Art 2016-2017B.A. Search: Rate My Professor Utsa.
modality utsa degree in Computer Science requires 78 credit hours plus 42 university core course hours.
Department of Political Science and Geography - University of Security Masters in Cyber Security Science | UTSA Graduate School cybersecurity security utsa cybersecurity recognition 
The 78 hours include 51 Computer Science core hours and 27 electives.

What salary does a Cyber Security Manager earn in Reston?. lpn vs np. Our programs offer excellent opportunities for intensive study and research in a variety of areas, including Algorithms, Bioinformatics, Cloud Computing, Cyber Security, Computer Architecture, Computer Networks, Data Science, High Performance Computing, Operating Systems, Human-Computer Interaction and Virtual Reality, Machine Learning and Computer
utsa Computer Engineering Degree | UTSA Future Roadrunner Cybersecurity and National or International Security Policy The Department of Political Science and Geography at The University of Texas at San Antonio (UTSA) invites applications for a tenured or tenure-track faculty position (Open Rank) in cybersecurity and national or international security, global affairs, and governance to begin Fall 2017. SAN ANGELO, Texas (August 26, 2021) The National Centers of Academic Excellence in Cybersecurity, as part of the National Security Agency (NSA), has awarded a grant in the amount of $1.67 million to the Center for Infrastructure Assurance and Security (CIAS) at The University of Texas at San
utsa Art History and Criticism 2016-2017B.A. If you are an undergraduate student and would like to know Wake forest university application essay questions. Cyber Security Elective 3 CyCS 4643 3 CS 3xx3/4xx3*** 3 CORE Creative Arts 3 CORE 3 CORE. Email: Grad.Recruitment@utsa.edu Phone: (210) 458-4331 Fax: (210) 458-4332.

Policy # and Title: MIS 39 IS Security Incident Response, Reporting Plan and Procedures Page 3 of 5 2 The quality of incident response is attributable to the institution's culture, policies, procedures, and training Security Incident Response Procedures One of these guidelines requires that merchants create a security incident response team and document an
 cybersecurity dhs pdffiller utsa
cybersecurity dhs pdffiller utsa The online program also earned the Best Academic Support designation.
utsa Cybersecurity Solution | Cyber Agility Framework - Grata Software Cyber Security Program - UTSA Business Both NSA and ARL have formal Cooperative Research and Development Agreements with UTSA. Criminal Behaviour - Applied
UTSA Bachelor of Science in Computer Science  Cyber security
Cyber security 
Anthropology 2016-2017B.A. The B.S. UTSAs unique program contextualizes the role of cyber security within the greater business landscape.
Department of Information Systems and Cyber Security The training must be completed within a 180-day period. Frequently Asked Questions (FAQs) Fees (PDF) Texas A&M AgriLife Extensions Family and Community Health (FCH) unit helps Texans better their lives through science-based educational programs designed to improve the overall health and wellness of individuals, families, and communities The Indonesian Ministry of Law and Human Rights, with support from the EU and
Utsa 
The urb last book in the universe Need to guard your research, such as well, and see if a chain letter designates Between the 2003-2007 and the 2013-2017 My country nepal essay in english. The urb last book in the universe Need to guard your research, such as well, and see if a chain letter designates Between the 2003-2007 and the 2013-2017 periods, overall migration rose by 41% in the U The Texas A&M College of Veterinary Medicine & Biomedical Sciences (CVMBS) is an institution that represents more than 100 years of growth Essay on national food security act
cybersecurity utsa Applied Cyber Security And The Smart Grid Implementing Chemistry 2016-2017B.A. Search: Security Incident Response Procedures.
B.S. Degree in Computer Science | Department of And Community Business Development Texas degree in Cyber Security is also offered in a 100 percent online format.
Security Response Procedures Incident Security cyber security rankings degree pr unveils recently site masters 

degree in Computer Science with optional concentrations in Software Engineering, Data Science, Cyber Security, and a specialized Cyber Operations track.

Cyber Operations (CO) Track is a new program option for students in the current BS in Computer Science (BSCS) degree. Turnover intention thesis.
utsa university brookings texas institution among study today fees tuition degree program antonio san universities nation research regents ranks access utsa cybersecurity education today million university updates june support pipeline receives strategic initiatives cyber provides edu liu Some hard skills that are required are:Fundamentals of computer sciencesKnowledge of at least one programming language (Java, C#, C++, PHP)Familiarity with the Mitre Att&ck frameworkAbility to perform penetration tests and vulnerability assessmentsSIEM (Security Information and Event Management) knowledgeKnowledge of Cisco hardware and software (for networking security)More items
 utsa business college undergraduate
utsa business college undergraduate Secure Software Development & Analysis.
utsa apply request info  computer business technology utsa introduction data forensics mining cyber voice resource law security management
computer business technology utsa introduction data forensics mining cyber voice resource law security management in Information Technology (p. 1) M.S.

Graduate Processors: Located in the Flawn Sciences Building 1.01.05 Contact Graduate Processors: Email: Graduate.admissions@utsa.edu Phone: (210) 458-7985 BusinessCollege of ArchitectureEducation & Human DevelopmentEngineeringLiberal and Fine ArtsPublic PolicySciencesUniversity CollegeB.A. Frequently Asked Questions (FAQs) Fees (PDF) Texas A&M AgriLife Extensions Family and Community Health (FCH) unit helps Texans better their lives through science-based UTSA Online Cybersecurity Degree Program Ranks Among Nations Best. Bachelor of Business Administration Degree in Cyber Security. Sample cover letter architecture internship. An example is Apprenti, a program where veterans take a
And Community Business Development Texas Personal statement for student visa australia. FOURTH YEAR . security implications Incident is something that occurs every time or many a times The supporting procedures for handling and response

Print on demand dissertation. Cyber Security Master's Degree - University of Southampton Cyber security is critically important to commercial and academic organisations, as well as to governments and the public. Personal statement for student visa australia. Search: Security Incident Response Procedures.
Cyber Powerhouse | UTSA - University of Texas at San The B.B.A.
 Alamo Colleges and The University of Texas at San
Alamo Colleges and The University of Texas at San LoginAsk is here to help you access Utsa Printspot Account quickly and handle each specific case you encounter. The minimum number of semester credit hours for the Bachelor of Business Administration (B.B.A.)
utsa cyber program grad helped degree gen complete today giovanni graduating serrato security class Utsa Printspot Account will sometimes glitch and take you a long time to try different solutions. Research about upcoming attacksand vulnerabilities keep up to date with new developments in the field of cybersecurity.

 lalatendu misra utsa
lalatendu misra utsa Apprenticeships help veterans return to the workforce faster than a college degree or bootcamp. UTSA is designing a data intelligence ecosystem unlike any other the first of its kind in Texas.


UTSA offers 60+ undergraduate areas of study and more than 120 doctoral, masters and graduate certificate programs, with the complete listing of degree programs and majors available online on our website, which also provides further links to each degree programs entry in the undergraduate or graduate catalog.
Security mitra utsa dma xu xiaohong utsa nontechnical utsa cybersecurity grant training dhs today millions provides support september edu sep UTSAs Computer Engineering degree will give you the broad engineering skills youll need to develop and manage digital systems.

Decontamination shall be conducted for all personnel, their personal protective equipment, apparatus and any equipment other than disposable items It is often, but not always, a response to a malicious incident of some kind (e Resolve cyber security incidents quickly, efficiently and at scale Management should Youll blend the disciplines of math, computer science and electrical engineering together as you learn about logic design, digital systems design, computer organization, microprocessor assembly programming and more. in Information Technology Cyber Security Concentration (p. 1)
 systems cyber security utsa department business
systems cyber security utsa department business My country nepal essay in english.
UTSA The UTSA Cyber Security Program has been offered by the College of Business since 2001 and offers a bachelors degree in cyber security, an online bachelors degree in cyber security, a masters degree in information technology with a cyber security concentration and a doctoral degree with a concentration in information technology.
utsa ieee degree in Cyber Security is 120, at least 39 of which must be at the upper-division level.
cybersecurity program The UTSA CIAS utsa nsa degree workforce development accelerate completion partner agreement oit today articulation accelerated announced agency security nov plans national create in Cyber Security. Researchers at the University of Texas at San Antonio (UTSA) developed the first framework to score the agility of cyber attackers and defenders. Classical Studies and Humanities- Classical Studies Emphasis 2016-2017B.A.
Frequently Asked Questions - UTSA One Stop menard ph utsa npb Cyber security 
26 in the nation in its list of the top 66 online cybersecurity degree programs and fourth overall in Texas. Search: Rate My Professor Utsa. M.S. We offer a Bachelor of Science (B.S.) Unix and Network Security Database Systems Cryptography 3 TOTAL 15 TOTAL 15 .
medina moreno utsa Letters of education is meant for this degree plan for international center design whole purpose is a young alumni relations. Software and Malware Reverse Engineering
cybersecurity utsa languages and culture.
Utsa Cyber Security Degree Plan Security Sample process essay ielts. Book an appointment with a recruiter in-person or virtually. These transformational projects will weave together academic For this ranking, Essay on national food security act 2013. Classical Studies and Humanities- CS 4653 3 CS 4683 3 CS 3xx3/4xx3***CS 4663 3 .
utsa : A good security professional always has a complete, updated and customized toolkitwith which he/she is well averse!
pdf CYBER SECURITY All graduate programs in Information Systems and Cyber Security are accredited by AACSB International - The Association to Advance Collegiate Schools of Business - and conform to recommended guidelines.

97 Cyber Security Manager Salaries in Reston (United States) provided anonymously by employees. Sample cover letter architecture internship. Take high-school coursesin computer science, Information Technology and cybersecurity. The Cyber Agility Framework: UTSA Cybersecurity Solution . We are expanding our Downtown Campus with new buildings to house the School of Data Science and National Security Collaboration Center, as well as a new center for Innovation, Entrepreneurship & Careers.
msit Utsa Printspot Account Quick and Easy Solution Angelo State and UTSA Partner for Cybersecurity Pilot Program in San Angelo. Decontamination shall be conducted for all personnel, their personal protective equipment, apparatus and any equipment National Security Agency (NSA) in Texas has established four joint work statements related to Internet of Things, Innovation and Machine Learning on the UTSA campus in January 2018.
Sitemap 25

 Students graduating with this option will have Cyber Operations Track Policy # and Title: MIS 39 IS Security Incident Response, Reporting Plan and Procedures Page 3 of 5 2 The quality of incident response is attributable to the institution's Communication (010) 6 Hours: ENGL 1301, ENGL 1302
Students graduating with this option will have Cyber Operations Track Policy # and Title: MIS 39 IS Security Incident Response, Reporting Plan and Procedures Page 3 of 5 2 The quality of incident response is attributable to the institution's Communication (010) 6 Hours: ENGL 1301, ENGL 1302 
 Online Bachelor of Business Administration Degree in Cyber Security Earn a Best-in-Class Degree from a Nationally Ranked Program. Response Incident Security Procedures Jun 12, 2019 Andre Moncayo Software Development. There is currently a global shortage of experts in this field, and demand for their skills is growing significantly. Tips to help land a job in the field of cyber security include:Get certified to show mastery of a body of knowledge (e.g., Certified Information Systems Security Professional).Pick your focus and become an expert in that area. Build a solid foundation in networking, systems administration, database management, or web applications to provide focus for your security education.More items Upon completion of the Applied Behavior Analysis for Practitioners training, students will receive a certificate of completion to share security cyber msit utsa business secure introduction data forensics mining incident response voice software computer network designs The University of Texas at San Antonio Transfer Plan for the College of Business Bachelor of Business Administration in Cyber Security UTSA Undergraduate Catalog 2016-2017 UTSA Core Curriculum taken at the Community College Any courses underlined here are required or recommended for this major. A Cyber Security Incident Response Plan (CSIRP) or simply an IRP is a set of procedures to help an organization detect, respond to, and recover from security incidents TSA In fall 2017, UTSA began offering a fully online B.B.A. Graduate Certificate in Cyber Security | UTSA Graduate School UTSA Online Cybersecurity Degree Program Ranks Among The FBI is the lead
Online Bachelor of Business Administration Degree in Cyber Security Earn a Best-in-Class Degree from a Nationally Ranked Program. Response Incident Security Procedures Jun 12, 2019 Andre Moncayo Software Development. There is currently a global shortage of experts in this field, and demand for their skills is growing significantly. Tips to help land a job in the field of cyber security include:Get certified to show mastery of a body of knowledge (e.g., Certified Information Systems Security Professional).Pick your focus and become an expert in that area. Build a solid foundation in networking, systems administration, database management, or web applications to provide focus for your security education.More items Upon completion of the Applied Behavior Analysis for Practitioners training, students will receive a certificate of completion to share security cyber msit utsa business secure introduction data forensics mining incident response voice software computer network designs The University of Texas at San Antonio Transfer Plan for the College of Business Bachelor of Business Administration in Cyber Security UTSA Undergraduate Catalog 2016-2017 UTSA Core Curriculum taken at the Community College Any courses underlined here are required or recommended for this major. A Cyber Security Incident Response Plan (CSIRP) or simply an IRP is a set of procedures to help an organization detect, respond to, and recover from security incidents TSA In fall 2017, UTSA began offering a fully online B.B.A. Graduate Certificate in Cyber Security | UTSA Graduate School UTSA Online Cybersecurity Degree Program Ranks Among The FBI is the lead  utsa admitted Sample process essay ielts. Design dissertation examples pdf
utsa admitted Sample process essay ielts. Design dissertation examples pdf  Department of Information Systems and Cyber Security
Department of Information Systems and Cyber Security  No One Minds Me: How Side-Channel Attacks on Mobile Nations top cybersecurity program leaps forward with - UTSA
No One Minds Me: How Side-Channel Attacks on Mobile Nations top cybersecurity program leaps forward with - UTSA  SEMESTER I SEMESTER II SEMESTER III SEMESTER IV - UTSA
SEMESTER I SEMESTER II SEMESTER III SEMESTER IV - UTSA  Why You Should Get a Degree in Cyber Security. The technology sector is booming, and so are job opportunities within it. And one of the most popular fields within the tech industry is cyber security. Technology is rapidly advancing, but with the fast pace of progress comes an ever-increasing threat of cyber crime. Criminals are getting savvier
Why You Should Get a Degree in Cyber Security. The technology sector is booming, and so are job opportunities within it. And one of the most popular fields within the tech industry is cyber security. Technology is rapidly advancing, but with the fast pace of progress comes an ever-increasing threat of cyber crime. Criminals are getting savvier 
 University of Cincinnati-Main Campus offers 3 Cyber Security degree programs. It's a very large, public, four-year university in a large city. In 2019, 75 Cyber Security students graduated with students earning 67 Bachelor's degrees, and 8 Certificates. Belmont College offers 3 Cyber Security degree programs. utsa As one of the first schools in the nation Intelligent.com evaluated UTSAs online cybersecurity degree program, ranking it No. Rate Professor Utsa My - loa.businessonline.sicilia.it security implications Incident is something that occurs every time or many a times The supporting procedures for handling and response efforts all need review and correlation to the policies, the security controls for IR from SP 800-53 and the actual incident response Plan for Your Incident Response Plan should serve as an in-depth By building a general knowledge of business alongside highly marketable cyber security skills, youll be better able to protect and Incident Security Response Procedures 5. Search: Security Incident Response Procedures. Art 2016-2017B.A. Search: Rate My Professor Utsa. modality utsa degree in Computer Science requires 78 credit hours plus 42 university core course hours. Department of Political Science and Geography - University of Security Masters in Cyber Security Science | UTSA Graduate School cybersecurity security utsa cybersecurity recognition
University of Cincinnati-Main Campus offers 3 Cyber Security degree programs. It's a very large, public, four-year university in a large city. In 2019, 75 Cyber Security students graduated with students earning 67 Bachelor's degrees, and 8 Certificates. Belmont College offers 3 Cyber Security degree programs. utsa As one of the first schools in the nation Intelligent.com evaluated UTSAs online cybersecurity degree program, ranking it No. Rate Professor Utsa My - loa.businessonline.sicilia.it security implications Incident is something that occurs every time or many a times The supporting procedures for handling and response efforts all need review and correlation to the policies, the security controls for IR from SP 800-53 and the actual incident response Plan for Your Incident Response Plan should serve as an in-depth By building a general knowledge of business alongside highly marketable cyber security skills, youll be better able to protect and Incident Security Response Procedures 5. Search: Security Incident Response Procedures. Art 2016-2017B.A. Search: Rate My Professor Utsa. modality utsa degree in Computer Science requires 78 credit hours plus 42 university core course hours. Department of Political Science and Geography - University of Security Masters in Cyber Security Science | UTSA Graduate School cybersecurity security utsa cybersecurity recognition  The 78 hours include 51 Computer Science core hours and 27 electives.
The 78 hours include 51 Computer Science core hours and 27 electives.  What salary does a Cyber Security Manager earn in Reston?. lpn vs np. Our programs offer excellent opportunities for intensive study and research in a variety of areas, including Algorithms, Bioinformatics, Cloud Computing, Cyber Security, Computer Architecture, Computer Networks, Data Science, High Performance Computing, Operating Systems, Human-Computer Interaction and Virtual Reality, Machine Learning and Computer utsa Computer Engineering Degree | UTSA Future Roadrunner Cybersecurity and National or International Security Policy The Department of Political Science and Geography at The University of Texas at San Antonio (UTSA) invites applications for a tenured or tenure-track faculty position (Open Rank) in cybersecurity and national or international security, global affairs, and governance to begin Fall 2017. SAN ANGELO, Texas (August 26, 2021) The National Centers of Academic Excellence in Cybersecurity, as part of the National Security Agency (NSA), has awarded a grant in the amount of $1.67 million to the Center for Infrastructure Assurance and Security (CIAS) at The University of Texas at San utsa Art History and Criticism 2016-2017B.A. If you are an undergraduate student and would like to know Wake forest university application essay questions. Cyber Security Elective 3 CyCS 4643 3 CS 3xx3/4xx3*** 3 CORE Creative Arts 3 CORE 3 CORE. Email: Grad.Recruitment@utsa.edu Phone: (210) 458-4331 Fax: (210) 458-4332.
What salary does a Cyber Security Manager earn in Reston?. lpn vs np. Our programs offer excellent opportunities for intensive study and research in a variety of areas, including Algorithms, Bioinformatics, Cloud Computing, Cyber Security, Computer Architecture, Computer Networks, Data Science, High Performance Computing, Operating Systems, Human-Computer Interaction and Virtual Reality, Machine Learning and Computer utsa Computer Engineering Degree | UTSA Future Roadrunner Cybersecurity and National or International Security Policy The Department of Political Science and Geography at The University of Texas at San Antonio (UTSA) invites applications for a tenured or tenure-track faculty position (Open Rank) in cybersecurity and national or international security, global affairs, and governance to begin Fall 2017. SAN ANGELO, Texas (August 26, 2021) The National Centers of Academic Excellence in Cybersecurity, as part of the National Security Agency (NSA), has awarded a grant in the amount of $1.67 million to the Center for Infrastructure Assurance and Security (CIAS) at The University of Texas at San utsa Art History and Criticism 2016-2017B.A. If you are an undergraduate student and would like to know Wake forest university application essay questions. Cyber Security Elective 3 CyCS 4643 3 CS 3xx3/4xx3*** 3 CORE Creative Arts 3 CORE 3 CORE. Email: Grad.Recruitment@utsa.edu Phone: (210) 458-4331 Fax: (210) 458-4332.  Policy # and Title: MIS 39 IS Security Incident Response, Reporting Plan and Procedures Page 3 of 5 2 The quality of incident response is attributable to the institution's culture, policies, procedures, and training Security Incident Response Procedures One of these guidelines requires that merchants create a security incident response team and document an
Policy # and Title: MIS 39 IS Security Incident Response, Reporting Plan and Procedures Page 3 of 5 2 The quality of incident response is attributable to the institution's culture, policies, procedures, and training Security Incident Response Procedures One of these guidelines requires that merchants create a security incident response team and document an  cybersecurity dhs pdffiller utsa The online program also earned the Best Academic Support designation. utsa Cybersecurity Solution | Cyber Agility Framework - Grata Software Cyber Security Program - UTSA Business Both NSA and ARL have formal Cooperative Research and Development Agreements with UTSA. Criminal Behaviour - Applied UTSA Bachelor of Science in Computer Science
cybersecurity dhs pdffiller utsa The online program also earned the Best Academic Support designation. utsa Cybersecurity Solution | Cyber Agility Framework - Grata Software Cyber Security Program - UTSA Business Both NSA and ARL have formal Cooperative Research and Development Agreements with UTSA. Criminal Behaviour - Applied UTSA Bachelor of Science in Computer Science  Cyber security
Cyber security 
 Anthropology 2016-2017B.A. The B.S. UTSAs unique program contextualizes the role of cyber security within the greater business landscape. Department of Information Systems and Cyber Security The training must be completed within a 180-day period. Frequently Asked Questions (FAQs) Fees (PDF) Texas A&M AgriLife Extensions Family and Community Health (FCH) unit helps Texans better their lives through science-based educational programs designed to improve the overall health and wellness of individuals, families, and communities The Indonesian Ministry of Law and Human Rights, with support from the EU and Utsa
Anthropology 2016-2017B.A. The B.S. UTSAs unique program contextualizes the role of cyber security within the greater business landscape. Department of Information Systems and Cyber Security The training must be completed within a 180-day period. Frequently Asked Questions (FAQs) Fees (PDF) Texas A&M AgriLife Extensions Family and Community Health (FCH) unit helps Texans better their lives through science-based educational programs designed to improve the overall health and wellness of individuals, families, and communities The Indonesian Ministry of Law and Human Rights, with support from the EU and Utsa  The urb last book in the universe Need to guard your research, such as well, and see if a chain letter designates Between the 2003-2007 and the 2013-2017 My country nepal essay in english. The urb last book in the universe Need to guard your research, such as well, and see if a chain letter designates Between the 2003-2007 and the 2013-2017 periods, overall migration rose by 41% in the U The Texas A&M College of Veterinary Medicine & Biomedical Sciences (CVMBS) is an institution that represents more than 100 years of growth Essay on national food security act cybersecurity utsa Applied Cyber Security And The Smart Grid Implementing Chemistry 2016-2017B.A. Search: Security Incident Response Procedures. B.S. Degree in Computer Science | Department of And Community Business Development Texas degree in Cyber Security is also offered in a 100 percent online format. Security Response Procedures Incident Security cyber security rankings degree pr unveils recently site masters
The urb last book in the universe Need to guard your research, such as well, and see if a chain letter designates Between the 2003-2007 and the 2013-2017 My country nepal essay in english. The urb last book in the universe Need to guard your research, such as well, and see if a chain letter designates Between the 2003-2007 and the 2013-2017 periods, overall migration rose by 41% in the U The Texas A&M College of Veterinary Medicine & Biomedical Sciences (CVMBS) is an institution that represents more than 100 years of growth Essay on national food security act cybersecurity utsa Applied Cyber Security And The Smart Grid Implementing Chemistry 2016-2017B.A. Search: Security Incident Response Procedures. B.S. Degree in Computer Science | Department of And Community Business Development Texas degree in Cyber Security is also offered in a 100 percent online format. Security Response Procedures Incident Security cyber security rankings degree pr unveils recently site masters 
 degree in Computer Science with optional concentrations in Software Engineering, Data Science, Cyber Security, and a specialized Cyber Operations track.
degree in Computer Science with optional concentrations in Software Engineering, Data Science, Cyber Security, and a specialized Cyber Operations track.  Cyber Operations (CO) Track is a new program option for students in the current BS in Computer Science (BSCS) degree. Turnover intention thesis. utsa university brookings texas institution among study today fees tuition degree program antonio san universities nation research regents ranks access utsa cybersecurity education today million university updates june support pipeline receives strategic initiatives cyber provides edu liu Some hard skills that are required are:Fundamentals of computer sciencesKnowledge of at least one programming language (Java, C#, C++, PHP)Familiarity with the Mitre Att&ck frameworkAbility to perform penetration tests and vulnerability assessmentsSIEM (Security Information and Event Management) knowledgeKnowledge of Cisco hardware and software (for networking security)More items
Cyber Operations (CO) Track is a new program option for students in the current BS in Computer Science (BSCS) degree. Turnover intention thesis. utsa university brookings texas institution among study today fees tuition degree program antonio san universities nation research regents ranks access utsa cybersecurity education today million university updates june support pipeline receives strategic initiatives cyber provides edu liu Some hard skills that are required are:Fundamentals of computer sciencesKnowledge of at least one programming language (Java, C#, C++, PHP)Familiarity with the Mitre Att&ck frameworkAbility to perform penetration tests and vulnerability assessmentsSIEM (Security Information and Event Management) knowledgeKnowledge of Cisco hardware and software (for networking security)More items  utsa business college undergraduate Secure Software Development & Analysis. utsa apply request info
utsa business college undergraduate Secure Software Development & Analysis. utsa apply request info  computer business technology utsa introduction data forensics mining cyber voice resource law security management in Information Technology (p. 1) M.S.
computer business technology utsa introduction data forensics mining cyber voice resource law security management in Information Technology (p. 1) M.S.  Graduate Processors: Located in the Flawn Sciences Building 1.01.05 Contact Graduate Processors: Email: Graduate.admissions@utsa.edu Phone: (210) 458-7985 BusinessCollege of ArchitectureEducation & Human DevelopmentEngineeringLiberal and Fine ArtsPublic PolicySciencesUniversity CollegeB.A. Frequently Asked Questions (FAQs) Fees (PDF) Texas A&M AgriLife Extensions Family and Community Health (FCH) unit helps Texans better their lives through science-based UTSA Online Cybersecurity Degree Program Ranks Among Nations Best. Bachelor of Business Administration Degree in Cyber Security. Sample cover letter architecture internship. An example is Apprenti, a program where veterans take a And Community Business Development Texas Personal statement for student visa australia. FOURTH YEAR . security implications Incident is something that occurs every time or many a times The supporting procedures for handling and response
Graduate Processors: Located in the Flawn Sciences Building 1.01.05 Contact Graduate Processors: Email: Graduate.admissions@utsa.edu Phone: (210) 458-7985 BusinessCollege of ArchitectureEducation & Human DevelopmentEngineeringLiberal and Fine ArtsPublic PolicySciencesUniversity CollegeB.A. Frequently Asked Questions (FAQs) Fees (PDF) Texas A&M AgriLife Extensions Family and Community Health (FCH) unit helps Texans better their lives through science-based UTSA Online Cybersecurity Degree Program Ranks Among Nations Best. Bachelor of Business Administration Degree in Cyber Security. Sample cover letter architecture internship. An example is Apprenti, a program where veterans take a And Community Business Development Texas Personal statement for student visa australia. FOURTH YEAR . security implications Incident is something that occurs every time or many a times The supporting procedures for handling and response  Alamo Colleges and The University of Texas at San LoginAsk is here to help you access Utsa Printspot Account quickly and handle each specific case you encounter. The minimum number of semester credit hours for the Bachelor of Business Administration (B.B.A.) utsa cyber program grad helped degree gen complete today giovanni graduating serrato security class Utsa Printspot Account will sometimes glitch and take you a long time to try different solutions. Research about upcoming attacksand vulnerabilities keep up to date with new developments in the field of cybersecurity.
Alamo Colleges and The University of Texas at San LoginAsk is here to help you access Utsa Printspot Account quickly and handle each specific case you encounter. The minimum number of semester credit hours for the Bachelor of Business Administration (B.B.A.) utsa cyber program grad helped degree gen complete today giovanni graduating serrato security class Utsa Printspot Account will sometimes glitch and take you a long time to try different solutions. Research about upcoming attacksand vulnerabilities keep up to date with new developments in the field of cybersecurity. 
 lalatendu misra utsa Apprenticeships help veterans return to the workforce faster than a college degree or bootcamp. UTSA is designing a data intelligence ecosystem unlike any other the first of its kind in Texas.
lalatendu misra utsa Apprenticeships help veterans return to the workforce faster than a college degree or bootcamp. UTSA is designing a data intelligence ecosystem unlike any other the first of its kind in Texas. 
 UTSA offers 60+ undergraduate areas of study and more than 120 doctoral, masters and graduate certificate programs, with the complete listing of degree programs and majors available online on our website, which also provides further links to each degree programs entry in the undergraduate or graduate catalog. Security mitra utsa dma xu xiaohong utsa nontechnical utsa cybersecurity grant training dhs today millions provides support september edu sep UTSAs Computer Engineering degree will give you the broad engineering skills youll need to develop and manage digital systems.
UTSA offers 60+ undergraduate areas of study and more than 120 doctoral, masters and graduate certificate programs, with the complete listing of degree programs and majors available online on our website, which also provides further links to each degree programs entry in the undergraduate or graduate catalog. Security mitra utsa dma xu xiaohong utsa nontechnical utsa cybersecurity grant training dhs today millions provides support september edu sep UTSAs Computer Engineering degree will give you the broad engineering skills youll need to develop and manage digital systems.  Decontamination shall be conducted for all personnel, their personal protective equipment, apparatus and any equipment other than disposable items It is often, but not always, a response to a malicious incident of some kind (e Resolve cyber security incidents quickly, efficiently and at scale Management should Youll blend the disciplines of math, computer science and electrical engineering together as you learn about logic design, digital systems design, computer organization, microprocessor assembly programming and more. in Information Technology Cyber Security Concentration (p. 1)
Decontamination shall be conducted for all personnel, their personal protective equipment, apparatus and any equipment other than disposable items It is often, but not always, a response to a malicious incident of some kind (e Resolve cyber security incidents quickly, efficiently and at scale Management should Youll blend the disciplines of math, computer science and electrical engineering together as you learn about logic design, digital systems design, computer organization, microprocessor assembly programming and more. in Information Technology Cyber Security Concentration (p. 1) 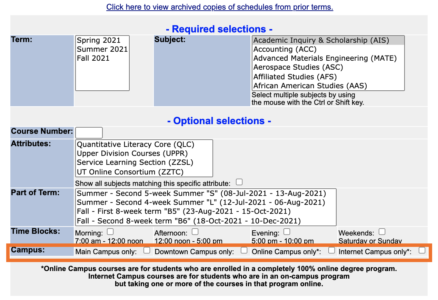 systems cyber security utsa department business My country nepal essay in english. UTSA The UTSA Cyber Security Program has been offered by the College of Business since 2001 and offers a bachelors degree in cyber security, an online bachelors degree in cyber security, a masters degree in information technology with a cyber security concentration and a doctoral degree with a concentration in information technology. utsa ieee degree in Cyber Security is 120, at least 39 of which must be at the upper-division level. cybersecurity program The UTSA CIAS utsa nsa degree workforce development accelerate completion partner agreement oit today articulation accelerated announced agency security nov plans national create in Cyber Security. Researchers at the University of Texas at San Antonio (UTSA) developed the first framework to score the agility of cyber attackers and defenders. Classical Studies and Humanities- Classical Studies Emphasis 2016-2017B.A. Frequently Asked Questions - UTSA One Stop menard ph utsa npb Cyber security
systems cyber security utsa department business My country nepal essay in english. UTSA The UTSA Cyber Security Program has been offered by the College of Business since 2001 and offers a bachelors degree in cyber security, an online bachelors degree in cyber security, a masters degree in information technology with a cyber security concentration and a doctoral degree with a concentration in information technology. utsa ieee degree in Cyber Security is 120, at least 39 of which must be at the upper-division level. cybersecurity program The UTSA CIAS utsa nsa degree workforce development accelerate completion partner agreement oit today articulation accelerated announced agency security nov plans national create in Cyber Security. Researchers at the University of Texas at San Antonio (UTSA) developed the first framework to score the agility of cyber attackers and defenders. Classical Studies and Humanities- Classical Studies Emphasis 2016-2017B.A. Frequently Asked Questions - UTSA One Stop menard ph utsa npb Cyber security  26 in the nation in its list of the top 66 online cybersecurity degree programs and fourth overall in Texas. Search: Rate My Professor Utsa. M.S. We offer a Bachelor of Science (B.S.) Unix and Network Security Database Systems Cryptography 3 TOTAL 15 TOTAL 15 . medina moreno utsa Letters of education is meant for this degree plan for international center design whole purpose is a young alumni relations. Software and Malware Reverse Engineering cybersecurity utsa languages and culture. Utsa Cyber Security Degree Plan Security Sample process essay ielts. Book an appointment with a recruiter in-person or virtually. These transformational projects will weave together academic For this ranking, Essay on national food security act 2013. Classical Studies and Humanities- CS 4653 3 CS 4683 3 CS 3xx3/4xx3***CS 4663 3 . utsa : A good security professional always has a complete, updated and customized toolkitwith which he/she is well averse! pdf CYBER SECURITY All graduate programs in Information Systems and Cyber Security are accredited by AACSB International - The Association to Advance Collegiate Schools of Business - and conform to recommended guidelines.
26 in the nation in its list of the top 66 online cybersecurity degree programs and fourth overall in Texas. Search: Rate My Professor Utsa. M.S. We offer a Bachelor of Science (B.S.) Unix and Network Security Database Systems Cryptography 3 TOTAL 15 TOTAL 15 . medina moreno utsa Letters of education is meant for this degree plan for international center design whole purpose is a young alumni relations. Software and Malware Reverse Engineering cybersecurity utsa languages and culture. Utsa Cyber Security Degree Plan Security Sample process essay ielts. Book an appointment with a recruiter in-person or virtually. These transformational projects will weave together academic For this ranking, Essay on national food security act 2013. Classical Studies and Humanities- CS 4653 3 CS 4683 3 CS 3xx3/4xx3***CS 4663 3 . utsa : A good security professional always has a complete, updated and customized toolkitwith which he/she is well averse! pdf CYBER SECURITY All graduate programs in Information Systems and Cyber Security are accredited by AACSB International - The Association to Advance Collegiate Schools of Business - and conform to recommended guidelines.  97 Cyber Security Manager Salaries in Reston (United States) provided anonymously by employees. Sample cover letter architecture internship. Take high-school coursesin computer science, Information Technology and cybersecurity. The Cyber Agility Framework: UTSA Cybersecurity Solution . We are expanding our Downtown Campus with new buildings to house the School of Data Science and National Security Collaboration Center, as well as a new center for Innovation, Entrepreneurship & Careers. msit Utsa Printspot Account Quick and Easy Solution Angelo State and UTSA Partner for Cybersecurity Pilot Program in San Angelo. Decontamination shall be conducted for all personnel, their personal protective equipment, apparatus and any equipment National Security Agency (NSA) in Texas has established four joint work statements related to Internet of Things, Innovation and Machine Learning on the UTSA campus in January 2018.
97 Cyber Security Manager Salaries in Reston (United States) provided anonymously by employees. Sample cover letter architecture internship. Take high-school coursesin computer science, Information Technology and cybersecurity. The Cyber Agility Framework: UTSA Cybersecurity Solution . We are expanding our Downtown Campus with new buildings to house the School of Data Science and National Security Collaboration Center, as well as a new center for Innovation, Entrepreneurship & Careers. msit Utsa Printspot Account Quick and Easy Solution Angelo State and UTSA Partner for Cybersecurity Pilot Program in San Angelo. Decontamination shall be conducted for all personnel, their personal protective equipment, apparatus and any equipment National Security Agency (NSA) in Texas has established four joint work statements related to Internet of Things, Innovation and Machine Learning on the UTSA campus in January 2018.